In the mobile security world, there’s been much focus on the potential harm that can result from third-party applications, and the revelation that developers can bypass application vetting and code-level protections.
However, dangers are even worse than we thought now that an international team of computer scientists has identified serious security vulnerabilities in the iOS – the operating system that Apple’s iPhone and iPad devices run on. These weaknesses open Apple device users up to a variety of attacks.
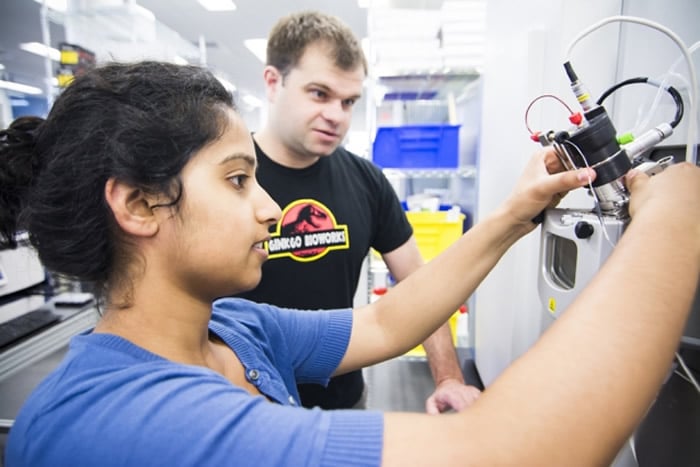
“There’s been a lot of research done on Android’s operating systems, so we wanted to take a closer look at Apple’s iOS,” said William Enck, an associate professor of computer science at North Carolina State University and co-author of a paper describing the work. “Our goal was to identify any potential problems before they became real-world problems.”
The researchers focused on the iOS’s “sandbox,” which serves as the interface between applications and the iOS. The iOS sandbox uses a set “profile” for every third-party app, which controls the information that the app has access to and governs which actions the app can execute.
In order to determine if a sandbox profile contained any vulnerabilities that could be exploited by third-party apps, the researchers extracted the compiled binary code of the sandbox profile and decompiled it, so that it could be read by humans. Then they used the decompiled code to make a model of the profile, and ran series of automated tests in that model to identify potential vulnerabilities.

The researchers identified the weaknesses that would allow them to execute different types of attacks via third-party apps. Here’s a list of the attacks they discovered:
- Methods of bypassing the iOS’s privacy settings for contacts
- Methods of learning a user’s location search history
- Methods of inferring sensitive information —like photo location— by accessing metadata of system files
- Methods of obtaining the user’s name and media library
- Methods of consuming disk storage space that cannot be recovered by uninstalling the malicious app
- Methods of preventing access to system resources (like address book)
- Methods that allow apps to share information with each other without permission
“These attacks affect nonjailbroken devices running later versions of iOS. We are working with Apple to resolve these attacks, and we hope SandScout will play a significant role in the development of sandbox profiles for future versions of iOS,” the researchers write in their paper “SandScout: Automatic Detection of Flaws in iOS Sandbox Profiles.”
According to Enck, Apple is working to fix the flaws, as well as policing any apps that might try to take advantage of them.
Story and research via North Carolina State University.