It was another successful event hosted by Hardware Pioneers, as a large group of technology enthusiasts eager to learn about bringing IoT products to market, from prototype to production came together.
Hardware Pioneers, a company that aim to connect and inspire professionals are building a smarter future in IoT, invited Microchip, Cypress Semiconductors and Koobe along to share their knowledge.
LoRa Product Line Manager at Microchip Technology, Jonathan Pearce started the evening off with the importance of authentication in LoRaWAN and other IoT applications and highlighting Metcalfe’s Law.
Metcalfe set out the law that scale leads to value, the systematic value of compatibility which allows communicating devices to grow as the square of their number. What is really important here is the internet. The internet for us is like oxygen – it is necessary. And although it is hard to put a number on it, the value of the internet is incredibly high.
IoT contrastingly is not quite there yet, as we see that the value of IoT has not yet risen above the cost. Volumes here are not quite high enough to take seriously, but you are going to need it to get anywhere – it’s a vicious circle, Pearce explained.
A recent study has shown that 70% of IoT devices have serious vulnerabilities, with two-thirds being considered unsecure. However, Pearce then asked the question: “Who cares?”
When you think about it, everyone knows security is essential, everyone is always talking about it – so why are some customers and clients not taking it seriously?
Many customers believe they have cracked IoT security with some simple A-B connections but this is far from correct.
What Pearce implored was something everyone can take away with them: CIA.
CIA
- Confidentiality
- Integrity
- Authentication
Security is achieved by most importantly Integrity and Authentication, the Confidentiality (encryption) is actually optional. If you stick to the rules of establishing the sender and ensuring the message is not altered in any way.
The Internet age
Today we face the constant battle of misinformation and fake news. If you take correct information out of context you can end up with fake news. If you don’t get clarification and factual evidence and do whatever you please with this misinformation you can end up with fake news. This is highly common with people who have powers of authority.
However, these are all Authentication and Integrity issues – we don’t need to clog up IoT with misinformation.
IoT can create complex interactions, not just node-to-cloud links. Pearce put it very simply: “IoT is not just A-B, it’s A-B-C-D-E… and external sources of information which are important as you deal with them every day.”
If we could eliminate human error we are eliminating stupidity and allowing IoT security to run much more smoothly.
Pearce then went on to discuss the five IoT security weaknesses and how we can solve them:
- Private keys are being protected by software at best, with passwords and other secrets held in-the-clear within the MCU or EEPROM memory.
Badly designed software which is running on a secure MCU/MPU can leave a system completely insecure – if you get hacked how do you know? If your identity is duplicated how do you know? If the system is misused how do you identify?
This is due to software security being insufficient, but can be solved by developing secure software which is complex and underestimated.
Hardware can secure elements. Many MCUs include architectural support: ‘Trustzone’ partitioned memory and crypto accelerators.
- Backdoors left opened to hackers – they attack the weakest point. Often in IoT, this means the unsecured hardware.
Standard devices include well understood backdoor vulnerabilities, and services exist providing cost and time effective extraction of secrets and IPs.
The solution is simple, again, hardware secures elements. With strong multi-level security:
- Active shield across multiple layers
- All memories internally
- Randomized math operations
- Internal state consistency checking
- Voltage tampers, isolated power rail
- Internal clock generation
- Secure test methods, no JTAG
- No debug probe points, no test pads
- A lack of large volume manufacturing scalability to upload device certificates. Keys/EUIs are being commissioned manually instead of scalable. The lack of scalability means symmetric keys are often handled manually and insecurely.
This is easily addressed with secure pre-commissioning via digital certificates.
- Security overhead is too much for battery and cost constrained devices – it is a common assumption that crypto is too computationally intensive. Another common assumption is that secure elements are cost prohibitive.
However, all it takes is efficiency of hardware accelerators to fix this problem.
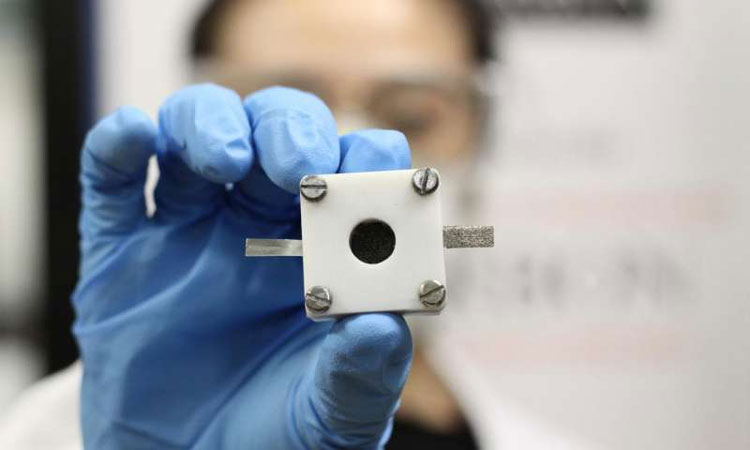
For example, same devices used in disposable consumer goods – printer cartridges: single wire interfaces, 2.5×6.5mm body, 0.5mm height and 2.0mm contact pitch. With a mechanical connector: non-electronic accessories and not intended for soldering.
- Device Firmware Updates (DFU) are rarely under full security control.
There are always hacks happening, for example, one of the latest hacks being the Mirai Botnet. However, if you identify the root of the trust and have high security storage you can gain more control with security.
Secondly Cypress Semiconductor’s IoT Regional Marketing Manager, David Armour came to educate us further in taking an IoT idea to production and the challenges and solutions you will face.
Cypress Semiconductor is focused on helping customers move from idea to production, as Armour drilled to a room full of entrepreneurs and professionals: “There is always a new platform, so you must prototype quickly.”
In order to succeed with this Armour shared a handy method to follow – WICED: Wireless Internet Connectivity for Embedded Devices.
Where do designs have problems?
Prototype hardware
You have to think about including the right hardware solution that can be taken to production.
Cost effectiveness – again you must consider if the chip level design is cheaper than the tested module. And of course think and look at the robustness and reliability of your product.
Can the solution be shipped to target regions?
Most evaluation software does not have regulatory approval and often will not comply.
How to deploy the product and support
- 1-100 units can update on a personal basis
- 100-1,000 units can be painful to support
- Realistically over 1,000 units is not scalable
Why is chip-on-board more expensive?
Modules reduce TTM, risk and cost – engineering test costs and risks are much higher with chip-on-board solutions. The entire process is virtually eliminated when using a module.
Regulatory certification costs are much higher and riskier – testing is time consuming and very expensive, it can be up to three to four months depending on the country, with bills as high as $25,000.
PCB costs are also higher – WLAN uses WLBGA and WLCSP packages for smaller designs and lower cost. These devices require six to eight layer PCBs with through-hole vias for four layer with blind/buried vias.
In a hyper-connected world, wireless connects people, clouds and devices to every’THING’.
Armour explained: “The environment is becoming crowded and 11ac provides more ‘air-time’ for all.”
The Industrial IoT needs 11ac for more robust, more reliable connections that have the latest security standards. It also provides an enterprise infrastructure which is AC so the network throughout is benefitted. Node density benefits from transmission speeds which allow for shorter on-air time and cleaner air.
Home and Consumer IoT needs 11ac, for its dual-band for mixed solutions, with Audio/Video entertainment and data. It provides beamforming for enhanced ranges, and provides better coexistence with crowded 2.4GHz band and BT/BLE devices – with improved network performance for multiple users as the cherry on the cake.
Armour concluded: “There are a lot of challenges and problems to fix with IoT, as there will always be embedded problems.”
Finally, the evening brought us Josh Lui, Director of Operation and Entrepreneurship at Koobe, who spoke to us all about the things he has personally learnt from his Foxconn veterans.
First thing Lui wanted to make extremely clear is that the production of hardware is not linear, and often when you have the wrong expectations you are likely to get dissatisfied.
There are two types of manufacturing – EMS (Electronics Manufacturing Service) and ODM (Original Design Manufacturing), and occasionally joint design manufacturing.
Lui explained that one issue that crops up a lot is the fact that many startups are getting these two the wring way round when approaching manufactures. This ends up wasting time for you and the manufacturer, but essentially was your own fault.
The engagement between customers and manufacturers can be conducted in two different ways:
- Deal with the subject straight on and talk to each other, ask for help and fully describe your needs, reaching out for help will be appreciated so you can fully understand each other’s needs.
- Or beforehand do your market research and walk in with confidence, as confidence sells.
One problem Lui was keen to iron out was the time scale for the budding developer. He said: “People go to crowdfunding too early and end up getting themselves into trouble before even reaching the Kickstarter stage.”
Lui left us with one final message – that you can’t just chose manufacturers based on their price, even though is seems like the best idea at the time it is not. “They will cut corners that will hurt you!”
The journey you and your IoT products go through from prototype to production may seem like a long winded complicated one, but if you follow the rules shared with us from the experts I am sure it will be more than worth it in the end.