Synopsys has announced version 8.7 of its Coverity static analysis tool with enhanced security analysis for mobile and web applications. Along with the recent acquisitions of Cigital and Codiscope, the latest version of the Coverity tool will provide Synopsys customers with the enterprise-level security analysis and broad programming language support necessary to address today’s evolving application security demands.
“Mobile and web applications are used widely across organizations to conduct business and process sensitive information, so addressing critical security vulnerabilities before they cause disruption for employees or customers is essential,” said Andreas Kuehlmann, Senior Vice President and general manager of Synopsys’ Software Integrity Group. “Given the rapid pace and scale of software development efforts today, detecting security flaws early in the development process with a highly accurate tool such as Coverity creates efficiencies that benefit all stakeholders.”
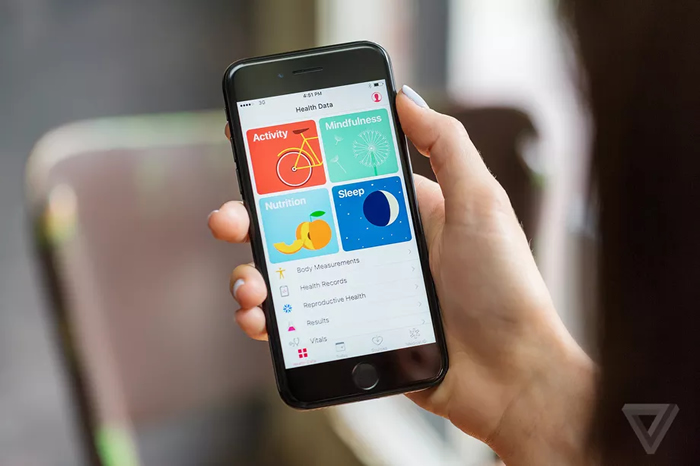
Mobile application security testing
A core component of the Synopsys Software Integrity Platform, the Coverity automated software testing tool analyzes source code to detect critical security vulnerabilities and defects early in the software development lifecycle. Coverity 8.7 includes major enhancements to the tool’s security analysis for Android applications, helping customers detect the most critical vulnerabilities and weaknesses on the OWASP Top 10.
Web application security testing
Coverity 8.7 also provides improved security analysis to detect a wider range of vulnerabilities in JavaScript, Java and C# web applications, and includes support for the new ECMAScript 6 scripting language specification. The JavaScript security analysis in Coverity 8.7 can be customized to improve the accuracy of testing results and reduce false positives and false negatives, which are common pitfalls for application security testing programs.
Secure software development lifecycle integration
The 8.7 version of the Coverity tool also expands and enhances its desktop analysis for mobile and web applications through plugins with popular Integrated Development Environments (IDEs) including Android Studio, Microsoft Visual Studio, IntelliJ and Eclipse. Developers will be able to perform security analysis from their desktop environment as part of a secure software development lifecycle for Android mobile applications and JavaScript and Node.js web applications. Developers will also be able to run quality analysis for other interpreted languages including PHP, Python and Ruby.
About the Synopsys software integrity platform
Through its Software Integrity Platform, Synopsys provides advanced solutions for improving software security and quality. This comprehensive platform of automated analysis and testing technologies integrates seamlessly into the software development process and enables organizations to detect and remediate quality defects, security vulnerabilities and compliance issues early in the software development lifecycle, as well as to gain security assurance with and visibility into their software supply chain.