Tampering with hardware used to read out information is a huge security risk. Researchers in Bochum developed a method to detect such manipulations—monitoring the systems with radio waves that react to the slightest changes in the ambient conditions. This method protects entire systems, not just individual components – at a lower cost. The RUB’s science magazine Rubin features a report by the team from Ruhr-Universität Bochum (RUB), the Max Planck Institute for Security and Privacy, and the IT company PHYSEC.
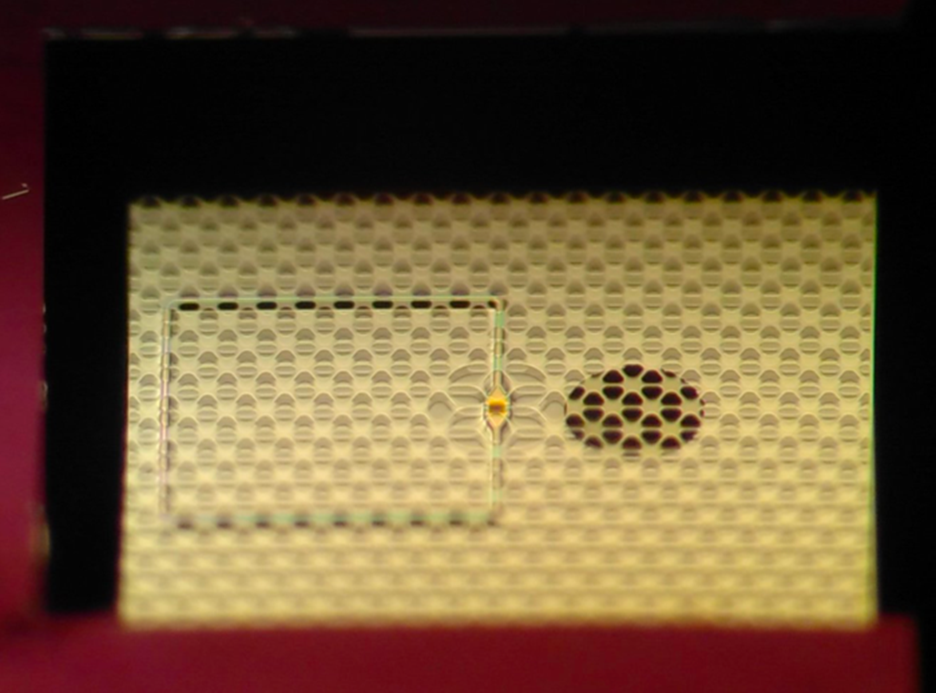
Scientists can use the radio wave technology to monitor an entire system. Researchers installed two antennas in the system: a transmitter and a receiver. The transmitter sends out a particular radio signal that spreads everywhere in the system, which reflects from the walls and computer components. All these reflections combine to create a fingerprint in the signal that reaches the receiver.
The team demonstrated in experiments that tiny changes to the system are enough to have a noticeable effect on the fingerprint. The IT experts equipped a conventional computer with radio antennas and punctured its housing with holes at regular intervals. Through these holes, the researchers let a fine metal needle penetrate the inside of the system and checked whether they noticed the change in the radio signal. In the process, they varied the thickness of the needle, the position, and penetration depth.
They reliably detected the penetration of a needle 0.3 millimeters thick with their system from a penetration depth of one centimeter. The system still detected a needle that was only 0.1 millimeters thick – but not in all positions. Placement of the antennas is critical.
Visit a detailed article on this topic in the IT Security special issue of the science magazine Rubin.